MFA/2FA and SSO are two leading contenders in this arena. But how do they stack up against each other, and which aligns best with your needs? This blog aims to shed light on these questions, offering insights into the pros, cons, and applications of each.
MFA/2FA: The Double-Check System
In an era where a single password no longer suffices, MFA (Multi-Factor Authentication) and 2FA (Two-Factor Authentication) emerge as enhanced security measures. By demanding multiple verification factors, they act as vigilant gatekeepers, ensuring that only authorized individuals gain access. Whether it's a combination of something you know, have, or are, MFA/2FA offers a dynamic and adaptable security solution. But, like all systems, they come with their own set of advantages and challenges.
Pros:
Enhanced Security: MFA/2FA significantly reduces the risk of unauthorized access by requiring multiple verification forms.
Flexibility: MFA/2FA can use various combinations like something you know (password), something you have (a phone or token), or something you are (fingerprint or facial recognition).
User Awareness: It keeps user’s alert. When a verification request pops up unexpectedly, it's a clear sign that someone might be trying to access their account.
Cons:
Inconvenience: Some users find it tedious to input multiple factors every time they log in.
Dependency on Devices: If you're using a phone as your second factor and it gets lost or runs out of battery, you could be locked out.
Potential for False Security: If not implemented correctly, users might feel overly secure and neglect other security practices.
SSO: One Key, Many Doors
Imagine a world where one key unlocks multiple treasures. That's the promise of SSO (Single Sign-On). By allowing users to log in once and gain access to a plethora of applications and services, SSO champions convenience.
However, with great power comes great responsibility. The very feature that makes SSO user-friendly can also be its Achilles' heel if managed incorrectly.
Pros:
User Convenience: Users love the simplicity of logging in just once to access all their apps.
Reduced Password Reset Requests: With fewer passwords to remember, there's a decrease in "forgot password" scenarios.
Enhanced User Experience: Seamless transitions between applications improve user satisfaction and productivity.
Cons:
Single Point of Failure: If a hacker gains access to the SSO credentials, they can potentially access all linked applications.
Complex Implementation: Setting up SSO can be intricate, requiring careful integration with all linked applications.
Potential Overlook of Individual App Security: With the focus on the main SSO login, security for individual applications might be overlooked.
MFA vs. SSO: What is the Difference?
The following explains the differences between MFA and SSO: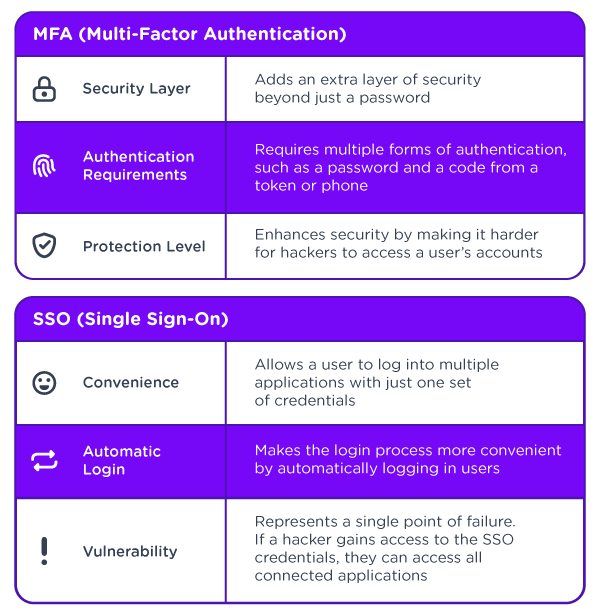
MFA vs. SSO: Which is More Secure?
Multi-Factor Authentication (MFA) and Single Sign-On (SSO) offer unique security advantages. MFA provides enhanced security by introducing additional authentication methods beyond the typical password. This approach has been known to thwart up to 99.9% of account breaches.
Conversely, SSO offers users the luxury of accessing multiple platforms with a singular credential set. While this streamlines the login process, it does present a vulnerability: should an attacker compromise these credentials, they might gain access to every linked application.
To sum up, MFA holds an edge regarding security with its multiple checks. However, when correctly set up and applied, both MFA and SSO offer robust security measures.
MFA and SSO: A Collaborative Approach to Security and User Experience
MFA and SSO serve unique purposes, but when integrated, they offer an enhanced blend of security and user-friendliness. Pairing MFA with SSO means users only need to sign in once with their credentials and subsequently confirm their identity through MFA to gain access to various applications and platforms.
Such a setup strikes the right balance between robust security and user convenience. Here's why:
MFA significantly bolsters the authentication process's security. However, it has its challenges. Users must remember their password and authenticate with an additional method, such as a code or OTP. This can make logging in a more prolonged ordeal.
Conversely, SSO offers a delightful user experience by allowing automatic access with a single credential set. But it presents a security risk – if attackers compromise the primary credentials, they potentially have access to all connected platforms.
By merging MFA and SSO, the strengths of one counterbalance the weaknesses of the other, creating an environment where security and user experience coexist harmoniously.
Here's a practical example using Active Directory and an Employee Portal to illustrate this synergy:
Users sign into their core application, like the Active Directory Employee Account.
The user attempts to access the employee portal, which houses sensitive data such as PII and financial records.
Due to SSO, the initial authentication step is automated because the user is already authenticated in their Active Directory Employee Account.
The portal then prompts a second-factor authentication – perhaps a push notification to the user's mobile.
After acknowledging the notification and verifying both authentication layers, the user gains access to the employee portal.
How Do You Know if SSO or MFA is the One to Choose for Your Business?
The choice between SSO and MFA is not merely a technical decision but one that reflects your business's core values and priorities. Understanding the unique needs, potential threats, and the nature of your operations can guide this decision. While some companies may lean towards the streamlined experience of SSO, others, especially those in sensitive sectors, might prioritize the robust security of MFA. However, the modern digital landscape often demands a blend of both, ensuring a seamless yet secure operational environment.
MFA/2FA and SSO have their parts to play in the intricate dance of digital security. While each offers distinct advantages, their combined strength can provide an unparalleled security framework. As businesses navigate the challenges of the digital age, understanding, adapting, and integrating these tools can pave the way for a safer, more efficient future. The key lies in informed choices, continuous adaptation, and a commitment to safeguarding data at all costs.