What is Online Identification?
Online identification refers to any bit of information associated with a specific individual found on the internet. While online identification is most often connected with entire personal accounts, such as banking profiles, it can consist of any personally identifiable information.
With the number of online services growing notably in recent years, online identification has become increasingly important. Previously, an individual may only have provided personal information for something like an email account. Today, however, online identification plays a key role in the delivery of age-dependent services like gambling sites, as well as allowing individuals to safely manage data relating to financial, medical, and many other industries.
What Types of Online Identification Are There?
Today, online identification is well established and an essential component for many businesses that need to be able to verify the identity of their customers, clients, or employees.

Although the terms identification, verification, and authentication are sometimes used interchangeably, they are actually slightly different. Identification simply refers to the act of claiming an identity. Verification, meanwhile, goes a step further and looks for a high degree of confidence in a person’s identity - perhaps through government-issued documents. Finally, authentication looks to re-validate an individual’s identity each time they use a particular service.
As new digital identification solutions have been developed, organizations have gained access to an increasingly diverse collection of tools with which to check the identities of particular individuals. These include the following:
Knowledge-based authentication - The simplest form of online identification, knowledge-based authentication asks users for a password or the answer to a security question in order to prove their identity. However, although this method of identification is the simplest for users, it is increasingly easy to falsify. Social engineering can be used by bad actors to acquire the sensitive information required to answer the relevant security questions and gain unauthorized access to a user’s account.
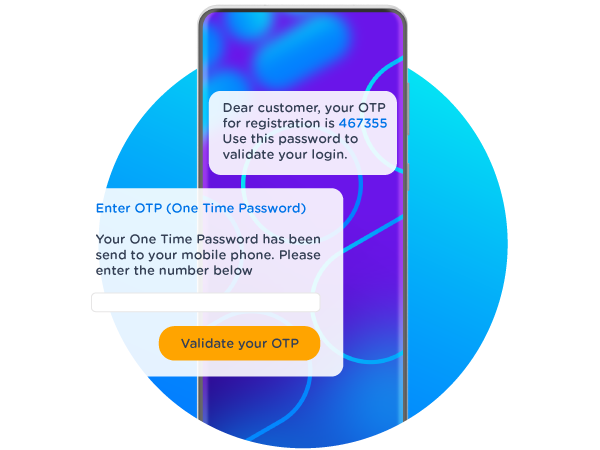
Two-factor authentication - All methods used for online identification have weaknesses that cyberattackers may look to exploit. As a result, some businesses have opted to employ two-factor authentication to verify an individual’s identity. Unlike digital solutions that only require a username-password pair in order to confirm a user’s identity, two-factor authentication, or 2FA, requires at least two pieces of “evidence” before online identification is confirmed. Generally, this evidence includes a combination of something a user knows, something a user has, and something a user is. One-time passwords, strings of characters or numbers automatically generated to be used for one single login attempt, are sometimes employed as part of a two-factor authentication approach.
iDIN - Some approaches to online identification leverage login methods used by other services to deliver robust security while streamlining the user journey. This is the case with iDIN, a service available in the Netherlands that allows individuals to use their bank’s login methods to access digital services provided by other organizations. For example, if a user wants to play the Dutch Lottery, they can select iDIN as a login method and use the trusted and secure credentials of their bank to provide substantial reliability about their identity. Once iDIN completes the online identification process, users are returned to their original online environment.
Biometric identification - Biometric identification uses an individual’s physical characteristics to verify their identity. Although it may sound slightly futuristic, biometric identification is already being used by some online services to authenticate online users by asking them for a photo of their face, a voice recording, or an image of their fingerprints. However, biometrics still comes with weaknesses and fraudsters are increasingly looking for ways of acquiring biometric information for malicious purposes.
Why Is Online Identification Important?
Online identification is the bedrock that underpins the modern digital economy. Being able to reliably authenticate users means businesses and consumers can trust that the individuals they are engaging with are who they say they are. Without this trust, banks, healthcare providers, social networks, forums, and a whole host of other online services could not guarantee privacy or security. Cybercrime continues to plague the online world, costing the global economy $6 trillion. Robust online identification can help bring this figure down.
What Are the Benefits of Online Identification?
As well as solidifying trust in online services, online identification provides several other benefits. For example, some incorporate age verification tools for businesses that only sell products to consumers above a certain age. What’s more, by employing a user-friendly, one-click verification tool, online identification can provide more certainty for businesses and increase conversion rates.
At CM.com, we use iDIN, and a number of other online identification tools to ensure businesses and consumers can enjoy the benefits of the digital economy in a simple and secure manner.